WIF With Bitbucket Pipelines
Workload Identity Federation (WIF) is becoming an important tool for developers looking to enhance the security of their CI/CD pipelines, particularly when working with third-party platforms like Bitbucket Pipelines. Static credential creation is an easy and often the go-to method for establishing access between cloud services and third-party applications. However, the problem with static keys is that they are vulnerable to credential leakage, privilege escalation, and information disclosure. If these keys are stolen, they can be used indefinitely and to prevent this, you must manually rotate your keys, which creates an operational overhead of having to change every key for every single service account in each application. Instead of relying on traditional static credentials, WIF uses short-lived tokens, reducing security risks by ensuring credentials are only valid for a limited time. This means you no longer need to worry about long-lived access keys being lost or exposed. WIF makes authentication to cloud services becomes more secure, streamlined, and manageable. It simplifies the process, making it easier for teams to focus on building and deploying code without the constant concern of managing service account keys.
Prerequisites
- A Bitbucket repository with Pipelines enabled and an account that has Admin role for the repository.
- Access to the GCP project with an account that has the Security Admin role.
Instructions
With that covered, here’s how you can easily set up workload identity federation between Bitbucket Pipelines and GCP:
- In Bitbucket:
a. Go to the repository page:
- From the left-hand menu, select “Repository Settings“
- Then scroll down and navigate to “OpenID Connect“
b. Choose the deployment environment you want to configure. For this guide, we will proceed with the “Production” deployment environment.
c. For next steps we are going to use:
- “Identity Provider URL” and “Audience” values under “Identity provider“
- Keys from “Example payload“ under “Unique identifiers“
- As well as the selected deployment environment UUID under “Deployment environments“.
Note that we will include the curly braces around the UUID values while using them in next steps. Example: {419097c3-XXXXXXXXXXXXX}
In GCP:
a. To access the Workload Identity Federation (WIF) page, do one of the following:
- From the left-hand menu, select “IAM & Admin” and then navigate to “Workload Identity Federation.”
- Use the top search bar to enter “Workload Identity Federation” and click on the matching result.
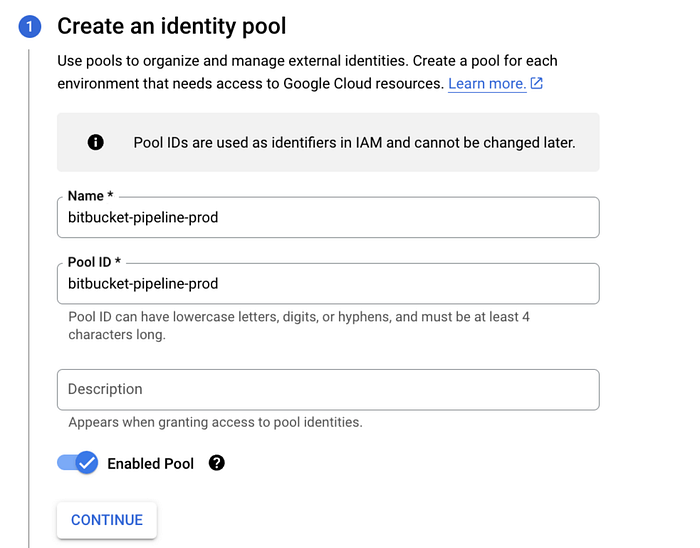
b. Create a workload identity pool by clicking the “Create Pool“ button at the top. We are going to call our pool “bitbucket-pipeline-prod”.
i. Enter the name bitbucket-pipeline-prod. Then click “Continue“. If you want, you can add a description to the pool, but it is not mandatory.
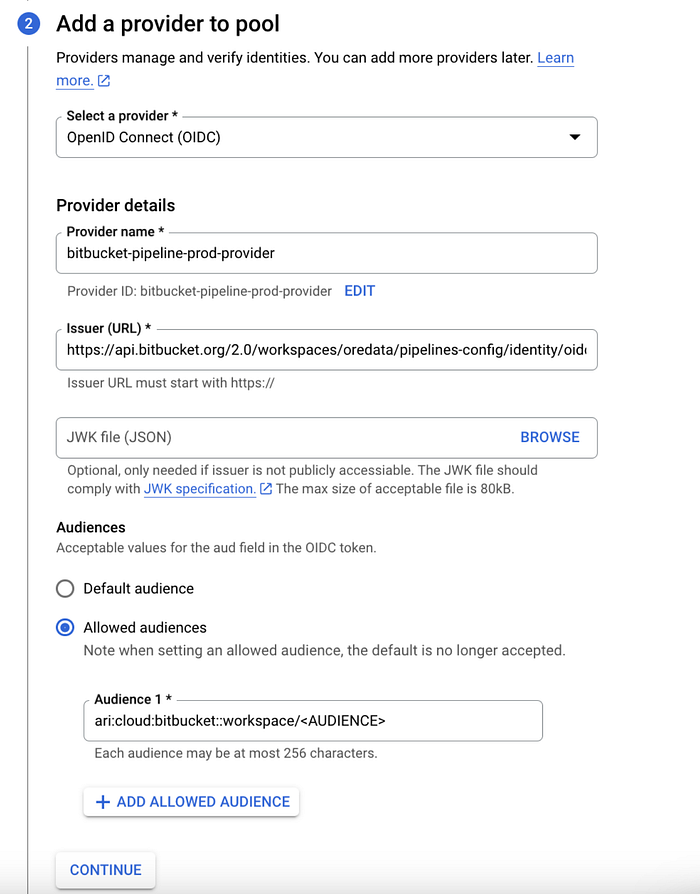
ii. On “Add A Provider To Pool“ form, click “Select A Provider“ from the options select “OpenID Connect“. After that, other inputs will appear on the screen.
iii. Under “Provider Details“:
- name the provider “bitbucket-pipeline-prod-provider”.
- Provide an id for the pool.
- Copy issuer URL from Bitbucket.
- Copy audience value from Bitbucket.
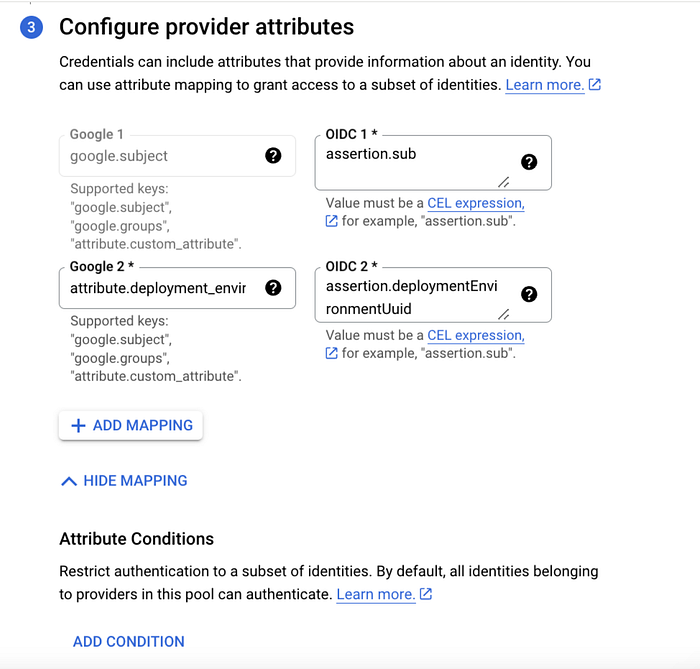
iv. Under “Configure Provider Attributes“ form:
- For “google subject” paste “assertion.sub”.
- Add “attribute.deployment_environment_uuid” and for the OIDC value, paste “assertion.deploymentEnvironmentUuid”. Any other value under Bitbucket’s “Unique Identifiers” tab can be added here. This depends on how access to the pool is configured.
v. Click the “Save” the provider.
c. Go to “bitbucket-pipeline-prod-pool” and choose “Grant access.”
i. Select “Grant access using Service Account impersonation“
ii. Select the service account to be used.
iii. Under “Select principals (identities that can access the service account)“, select the “deployment_environment_uuid” field from the left-hand side and copy the environment UUID from Bitbucket and paste its value. If any other field is used, then paste their value.

iv. Click “Save”.
d. In the next window, Select the created provider “bitbucket-pipeline-prod-provider”.
e. Enter /tmp/oidc-token.txt into the “OIDC ID token path” field. This will be used in subsequent steps.
f. Make sure the “Format type” is set to “text” because the authentication token that pipelines use ($BITBUCKET_STEP_OIDC_TOKEN) is a plain text token.
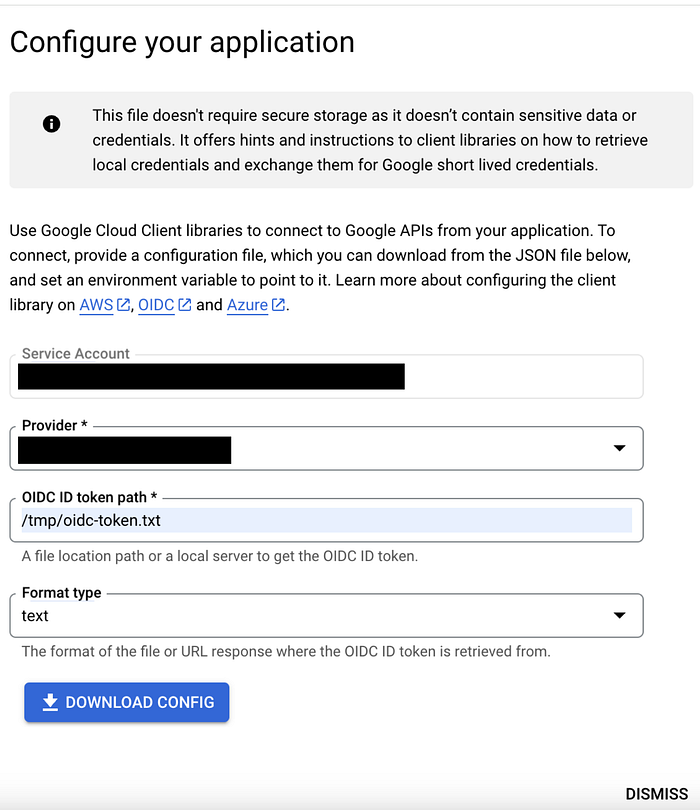
g. Download the config file, name it credentials.json and using openssl command base64 encode it.
openssl enc -A -base64 credentials.json
Save the output and make sure the result of this command is a single line.
- Back to Bitbucket:
Under “Repository Settings/Respository Variables“, create a variable called “GCLOUD_API_KEYFILE”. You can create separate variables for separate environments like “GCLOUD_API_KEYFILE_PROD“.
- In bitbucket-pipelines.yml
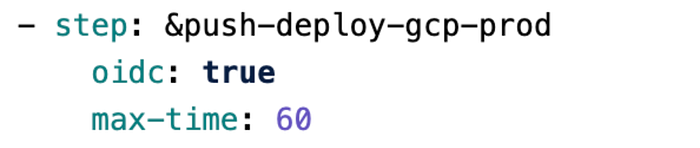
Add “oidc: true“ and “max-time: 60“ to the pipeline yaml.
- Add a step like:
echo "$BITBUCKET_STEP_OIDC_TOKEN" > /tmp/oidc-token.txt
- Then decode the encoded JSON credential file with:
echo $GCLOUD_API_KEYFILE | base64 --decode --ignore-garbage > ./gcloud-api-key.json
- Set GOOGLE_APPLICATION_CREDENTIALS for ADC with:
export GOOGLE_APPLICATION_CREDENTIALS=`pwd`/gcloud-api-key.json
- Finally authenticate and set project using:
gcloud auth login --cred-file=./gcloud-api-key.json
gcloud config set project $GCLOUD_PROJECT

Conclusion
Using Workload Identity Federation (WIF) in your CI/CD pipelines, especially with platforms like Bitbucket Pipelines, is a smart way to handle the security risks that come with old methods like static credentials. Instead of relying on long-lasting access keys, WIF uses short-term tokens, which helps protect against issues like stolen credentials and unauthorized access. It also saves developers the trouble of constantly updating keys manually, allowing them to focus more on building and deploying code. With WIF, teams can simplify their processes, improve security, and keep everything running smoothly with less effort and stress. In today’s fast-paced DevOps world, WIF is a useful tool for keeping your systems both secure and efficient.
Authors: Baran Hocaoğlu, Software Developer, Oredata
Zeyd Bora, Software Developer, Oredata
Oredata is a premier Google Cloud Partner and Managed Services Provider specialized in
- Cloud Migration Services
- Data & Analytics Services
- Application Development Services
- Infrastructure Services
- Google Workspace
If you are interested joining us, feel free to apply our job openings: https://www.linkedin.com/company/oredata/jobs/

 English
English Türkçe
Türkçe العربية
العربية